While scrolling my timeline on some social medium one day quite some time ago, I bumped into a post by (then) Offensive Security advertising a new version of Kali called 'Kali Purple'. I watched the linked video and realised it was actually a plug for their new course, 'SOC-200' targeting... blue teamers! OffSec doing DefSec?, I thought, that would be interesting...
While scrolling my timeline on some social medium one day quite some time ago, I bumped into a post by (then) Offensive Security advertising a new version of Kali called 'Kali Purple'. I watched the linked video and realised it was actually a plug for their new course, 'SOC-200' targeting... blue teamers! OffSec doing DefSec?, I thought, that would be interesting...
Many moons later, when the itch for a new challenge reemerged, I came to the conclusion that some technical upskilling in defensive ops would probably be more beneficial than an offensive one (you're next, CRTO) given the amount of time I was now spending with client SOCs. After some discussions with the bosses, I was given the thumbs up for this new and unknown OffSec offering, along with an extra request to note down some thoughts if I were to take it, in case others would be interested in the future but wanted an extra view.
So in May 2023, when the first gap in schedule appeared, I activated my 3-month lab access immediately. A large-scale Windows-focused Purple team had just been scheduled for late July and in the back of my mind this posed as a deadline, as it would require all the prep and upskilling I could get.
And so the adventure began. After exactly 2 months and 2 days, I passed the exam and got my third shiny OffSec cert (figuratively, as they sadly no longer do paper certs). Once the obligatory celebrations were out' the way, it was time to write it all down.
Read more…
 Briefly after finishing the Cloud Resume Challenge I discovered a few "Extensions" to the challenge were now provided. The extension which piqued my interest was the terraform one, due to the popularity of the Hashicorp technology among the community. The goal was simple: Convert your Infrastructure as Code (IaC) definition to terraform.
Briefly after finishing the Cloud Resume Challenge I discovered a few "Extensions" to the challenge were now provided. The extension which piqued my interest was the terraform one, due to the popularity of the Hashicorp technology among the community. The goal was simple: Convert your Infrastructure as Code (IaC) definition to terraform.
In my case, this meant porting the AWS Serverless Application Model (SAM) Template to terraform configuration, so that it could be deployed using just terraform init && terraform apply instead of the AWS-specific sam build && sam deploy workflow.
In late November, I was booked on a client assessment which included a terraform code review component, so what better opportunity to familiarise myself ahead of the job? So after just over a month and moments before 2022 waved goodbye, I completed the challenge extension and as part of step 15 I wrote a blog post to document what I learnt. The terraform clone of my Cloud Resume application can be found at https://resume.tf.laripping.com.
Read more…
 I strongly believe that to learn is to do. And having the longing itch to cover my deficiency in cloud security and cloud in general, it came as a big A-Ha moment when I read about the Cloud Resume Challenge in Nick Jones' awesome "Breaking Into Cloud" checklist.
I strongly believe that to learn is to do. And having the longing itch to cover my deficiency in cloud security and cloud in general, it came as a big A-Ha moment when I read about the Cloud Resume Challenge in Nick Jones' awesome "Breaking Into Cloud" checklist.
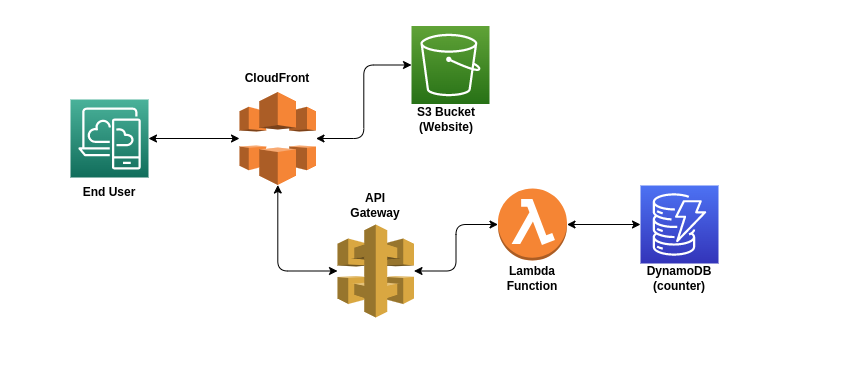
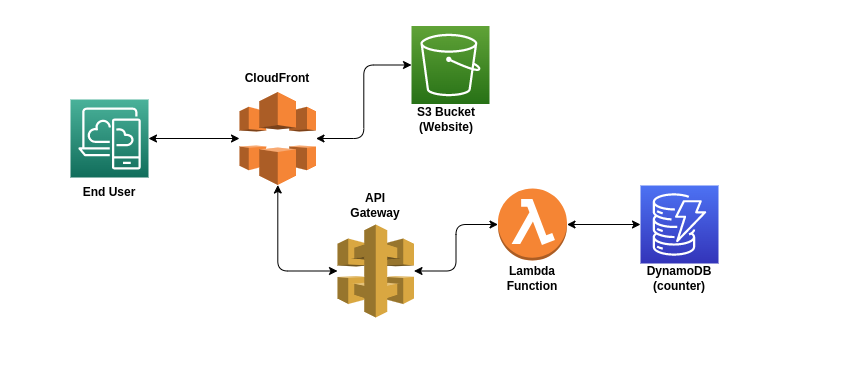
Essentially, the Cloud Resume Challenge is to create a simple web application, but fully cloud-native and using modern DevOps practices. The app will be a statically hosted website showing your Resumé (or just Resume from here onwards, might also use the term CV interchangeably) and will include some backend functionality in the form of a visitor counter. All of this will be created through 15 well-defined tasks.
Read more…
A mantra I've always followed is that if a certain problem has come up twice, you probably need to write the solution down somewhere. Scripta manent, as they say.
After delivering a few conference talks in the age of the pandemic, I found myself bumping over the same challenges again and again. While at the same time, I can recall being asked at least twice about the software I used or how to approach the overall workflow. This short article will therefore serve as a braindump of all the tips and tricks worth noting, to skip the hustle next time or maybe help others figure their way out.
Read more…
 Recently, while doing some Android reverse engineering, I bumped into the following problem: After digging into the decompiled Java code, my analysis for the functionality of interest led me to a native function... which was nowhere to be found in the disassembly of the respective .so library. What sorcery is this? And where on god's green earth is my native function in that massive ELF blob?
Recently, while doing some Android reverse engineering, I bumped into the following problem: After digging into the decompiled Java code, my analysis for the functionality of interest led me to a native function... which was nowhere to be found in the disassembly of the respective .so library. What sorcery is this? And where on god's green earth is my native function in that massive ELF blob?
In this blog post I will therefore:
- Explain why sometimes JNI functions don't pop up in the Function Listing, and most importantly
- Present a novel technique to 'enrich' the disassembly with these functions' signatures ...wait for it... using Frida!
Read more…
 While scrolling my timeline on some social medium one day quite some time ago, I bumped into a post by (then) Offensive Security advertising a new version of Kali called 'Kali Purple'. I watched the linked video and realised it was actually a plug for their new course, 'SOC-200' targeting... blue teamers! OffSec doing DefSec?, I thought, that would be interesting...
While scrolling my timeline on some social medium one day quite some time ago, I bumped into a post by (then) Offensive Security advertising a new version of Kali called 'Kali Purple'. I watched the linked video and realised it was actually a plug for their new course, 'SOC-200' targeting... blue teamers! OffSec doing DefSec?, I thought, that would be interesting...